Solutions Architect Interview Questions in 2026: What Hiring Panels Actually Ask

Most lists of "solutions architect interview questions" are recycled AWS exam prep with a few system-design prompts taped on. That's not what 2026 panels are testing. The exam-style recall round still exists, but it's now one of four rounds at most. The other three are where offers are won and lost.
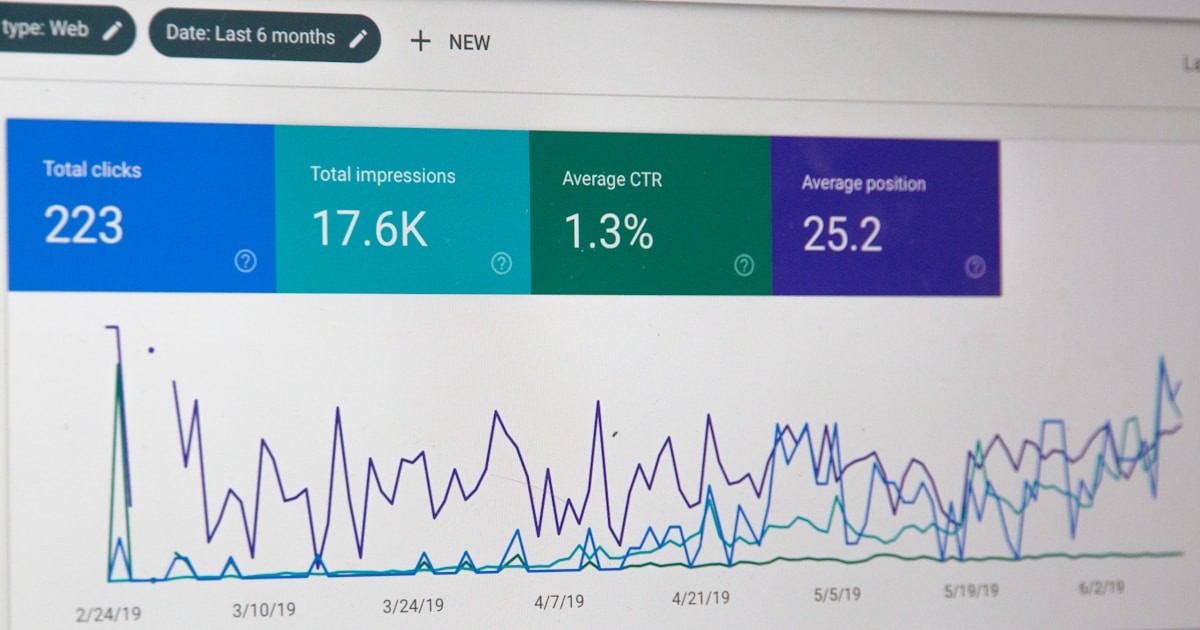
Across the candidates running mock solutions-architect rounds on LastRound AI in Q1 2026, the strongest signal of who got the offer wasn't depth of AWS service knowledge. It was the ability to answer a clean technical question, then re-answer it for a non-technical executive without flinching. The "translate this for a CFO" follow-up is the new whiteboard.
Below: the questions that come up most often right now, grouped by the round they show up in, with what panels are listening for. Specific numbers where they matter. No 80-question dumps.
Round 1: The cloud fundamentals screen
This is the call where you get rejected for hand-wavy answers about availability zones. It's usually 45 minutes with a senior architect or staff engineer. Three questions show up almost every time.
"Walk me through how you'd design for multi-region failover." The wrong answer is a list of AWS services. The right answer starts with RTO and RPO targets, then picks an active-passive vs active-active model, then names the data-replication strategy and what it costs in latency. If you skip RTO/RPO, the panel writes "no business context" in their notes and you're done.
"How would you reduce a $200k/month AWS bill by 30%?" Real numbers like this are now standard. Flexera's 2024 State of the Cloud report found that organizations waste 27% of their cloud spend on average. Panels want to hear: tag audit first, then right-size compute, then reserved instances or Savings Plans for the predictable baseline, then spot for batch. Skip storage-class lifecycle policies and you'll miss what everyone names as the easiest 15%.
"AWS vs Azure vs GCP for a new workload, how do you choose?" The trap is reciting marketing pages. The signal is: what's the existing skill set, what's the data-gravity story, what compliance regimes does the workload sit under. Strong answers cite specific cases where the "obvious" choice flips. (Heavy BigQuery shop? GCP wins on data even if everything else is AWS.)
Round 2: System design with a business twist
The classic 60-minute whiteboard. Same as a senior engineer system design round, with one extra wrinkle: the prompt usually carries a business constraint that you can't ignore. "Design a multi-tenant SaaS billing system, and tell me how you keep per-tenant costs flat as we 10x customers." The billing-system part is table stakes. The cost-per-tenant answer is what separates SA candidates from SWE candidates.
Other prompts that come up often right now:
- Design a global content-delivery system for a streaming product (Netflix-style). Edge caching, origin shield, fail-open vs fail-closed when CDN nodes go dark.
- Design the read path for a financial-data feed used by 200 internal services. Cache invalidation, fan-out, and the "what if we get the price wrong by a penny" failure mode.
- Design an event-driven order processor that has to be exactly-once. Idempotency keys, the outbox pattern, what you'd skip if the team was four engineers instead of forty.
One thing that's shifted since 2023: panels expect you to name specific managed services and explain when you'd not use them. "I'd use SQS" with no follow-up reads as shallow. "I'd use SQS with a DLQ at 5 retries, and I'd swap to Kinesis if ordering becomes a hard requirement" reads as senior.
Round 3: The stakeholder round (where most candidates fail)
Usually 45 minutes with a PM, eng director, or VP. No whiteboard. The question is typically a variation of: "We just gave you the design from round 2. Explain it to a CFO who needs to sign off on a $4M migration. You have ten minutes."
The candidates who win this round don't try to dumb the architecture down. They reframe it. Three patterns work:
- Lead with the dollar number and the risk: "This costs $4M over 18 months. Without it, we estimate $600k/month in downtime risk by Q3."
- Use one analogy, not five. Pick the one closest to a domain the executive already runs (logistics, supply chain, real estate).
- Show two options, not one. Executives reject single-option pitches by reflex. Give them an A and a B and let them pick.
The candidates who lose this round either dive into technical jargon, or worse, oversimplify to the point of being patronizing. The director will ask one clarifying question to test if you actually know it. If your answer isn't credible, you're done.
Round 4: Security and compliance scenarios
Shorter round, usually 30 minutes, often with the security architect or a CISO delegate. Three scenarios come up repeatedly.
"A vendor we use leaked customer PII. Walk me through the next 24 hours." The expected answer isn't a playbook recital. It's: identify scope, contain, communicate (internal + external), preserve forensics, start regulatory clock. The detail that gets noted: do you know the GDPR 72-hour window? Do you know what "without undue delay" means under California's CCPA?
"How would you set up secrets management for a 200-engineer org migrating off hardcoded values?" Centralized vault (Secrets Manager, Vault, Doppler), short-lived credentials wherever possible, automated rotation, audit trail. The thing candidates skip: how you'd run the migration without a multi-week freeze.
"Walk me through zero-trust for a hybrid environment." Identity-first (every request authenticated), micro-segmentation, continuous verification. The 2026-specific follow-up: what changes when AI agents are calling your APIs? It's a real question, not a hypothetical. Most large orgs are hitting it now. The CNCF 2024 survey shows 76% of organizations are running production AI workloads, and most haven't updated their auth model for non-human callers.
What the questions test (and what panels actually score)
We pulled feedback from 92 solutions-architect mock rounds run on LastRound AI between January and March 2026. The questions vary; the rubric doesn't. Five things show up in almost every scorecard:
- Did the candidate ask about non-functional requirements before designing? (RTO, RPO, throughput, latency budget, compliance.) Missing this = automatic mid-rating.
- Did they name dollar costs anywhere? Senior SA roles assume you can ballpark to the right order of magnitude. "Roughly $80k/month for this region" is fine. "Some monthly cost" is not.
- Did they reject any approach? Candidates who say yes to everything score poorly. Saying "I wouldn't use Kafka here because..." is a strong positive signal.
- Did they explain a failure mode? What breaks first, what breaks second, what user impact looks like.
- Did they switch register? When the panelist asks a vague "how would you tell the CEO?" question, did the candidate actually change vocabulary?
Two of these (3 and 5) are the ones AI tools currently struggle to coach. That's where mock interviews still beat flashcards.
One thing I'd skip
The "AWS Well-Architected Framework five pillars" recital. Every candidate I've seen do this verbatim got a polite nod and lost ground. Panels know the pillars. They want to hear how you applied them in something that actually ran in production. A specific story about how you traded reliability against cost on a real workload beats the framework name-drop every time.
Honestly, if I were starting prep from zero today, I'd spend one week on the Well-Architected Framework for the language, then four weeks on practicing the stakeholder round and the cost-modeling round. Those are the differentiated parts and they're under-practiced.
Written by
Shekhar
LastRound AI
On the LastRound AI team. Writes about career advice, behavioral interviews, and how to navigate hiring at startups and big tech.
Further reading
- The Muse — STAR method guide — How to structure behavioural answers
- Tech Interview Handbook — Free, open-source interview prep
- Cracking the Coding Interview — Industry-standard prep book reference
Share this post
Related articles
Interview Q&A
50 API Developer Interview Questions & Answers 2026 (REST, GraphQL, Design) | LastRound AI
Interview Q&A
35+ Account Executive Interview Questions 2026 (Enterprise Sales) | LastRound AI
Interview Q&A
30+ Blockchain Developer Interview Questions & Answers 2026 (Smart Contracts & Web3) | LastRound AI
Interview Q&A
35+ Business Analyst Interview Questions That Actually Matter (2026 Guide) | LastRound AI